Compliance
Compliance Automation,
Not Compliance Theater
13 of 18 CIS Controls automated out of the box. No add-ons, no manual spreadsheets, no quarterly scrambles. Continuous enforcement with audit-ready evidence from the same platform that manages your endpoints.
CIS Controls v8 Coverage Map
Control-by-control breakdown of what Breeze automates, what requires integration partners, and what falls outside RMM scope.
| CIS | Control | Status | Breeze Coverage |
|---|---|---|---|
| Foundation Controls (CIS 1-6) | |||
| 1 | Enterprise Asset Inventory | Automated | Continuous hardware/OS/network discovery via agent heartbeat |
| 2 | Software Asset Inventory | Automated | Real-time installed software tracking with change detection |
| 3 | Data Protection | Automated | Encryption verification, data-at-rest posture checks |
| 4 | Secure Configuration | Automated | Configuration policies with drift detection and auto-remediation |
| 5 | Account Management | Automated | Local account enumeration, privilege auditing, stale account detection |
| 6 | Access Control Management | Automated | Role-based access, MFA enforcement tracking, admin right monitoring |
| Operational Controls (CIS 7-12) | |||
| 7 | Continuous Vulnerability Management | Automated | Patch status tracking, missing update detection, risk scoring |
| 8 | Audit Log Management | Automated | Centralized log collection with defined retention and search |
| 9 | Email & Web Browser Protections | Partial | Browser configuration policies; email filtering via integration |
| 10 | Malware Defenses | Automated | AV/EDR status monitoring, definition currency, quarantine alerts |
| 11 | Data Recovery | Automated | Backup status verification, recovery testing, retention validation |
| 12 | Network Infrastructure Management | Automated | SNMP monitoring, network device configuration, topology awareness |
| Response Controls (CIS 13-18) | |||
| 13 | Network Monitoring & Defense | Automated | Traffic baseline monitoring, anomaly detection, alert correlation |
| 14 | Security Awareness & Skills Training | Partial | Training completion tracking via integration; delivery requires partner |
| 15 | Service Provider Management | Partial | Vendor inventory tracking; contract management via integration |
| 16 | Application Software Security | Partial | Application inventory and update tracking; SAST/DAST via integration |
| 17 | Incident Response Management | Automated | Automated IR workflows, timeline reconstruction, evidence packaging |
| 18 | Penetration Testing | N/A | Out of scope for RMM platforms; requires specialized engagement |
Foundation Controls (CIS 1-6)
Enterprise Asset Inventory
Continuous hardware/OS/network discovery via agent heartbeat
Software Asset Inventory
Real-time installed software tracking with change detection
Data Protection
Encryption verification, data-at-rest posture checks
Secure Configuration
Configuration policies with drift detection and auto-remediation
Account Management
Local account enumeration, privilege auditing, stale account detection
Access Control Management
Role-based access, MFA enforcement tracking, admin right monitoring
Operational Controls (CIS 7-12)
Continuous Vulnerability Management
Patch status tracking, missing update detection, risk scoring
Audit Log Management
Centralized log collection with defined retention and search
Email & Web Browser Protections
Browser configuration policies; email filtering via integration
Malware Defenses
AV/EDR status monitoring, definition currency, quarantine alerts
Data Recovery
Backup status verification, recovery testing, retention validation
Network Infrastructure Management
SNMP monitoring, network device configuration, topology awareness
Response Controls (CIS 13-18)
Network Monitoring & Defense
Traffic baseline monitoring, anomaly detection, alert correlation
Security Awareness & Skills Training
Training completion tracking via integration; delivery requires partner
Service Provider Management
Vendor inventory tracking; contract management via integration
Application Software Security
Application inventory and update tracking; SAST/DAST via integration
Incident Response Management
Automated IR workflows, timeline reconstruction, evidence packaging
Penetration Testing
Out of scope for RMM platforms; requires specialized engagement
13 controls fully automated. 4 supported via integrations. Only penetration testing (CIS 18) falls outside RMM scope entirely.
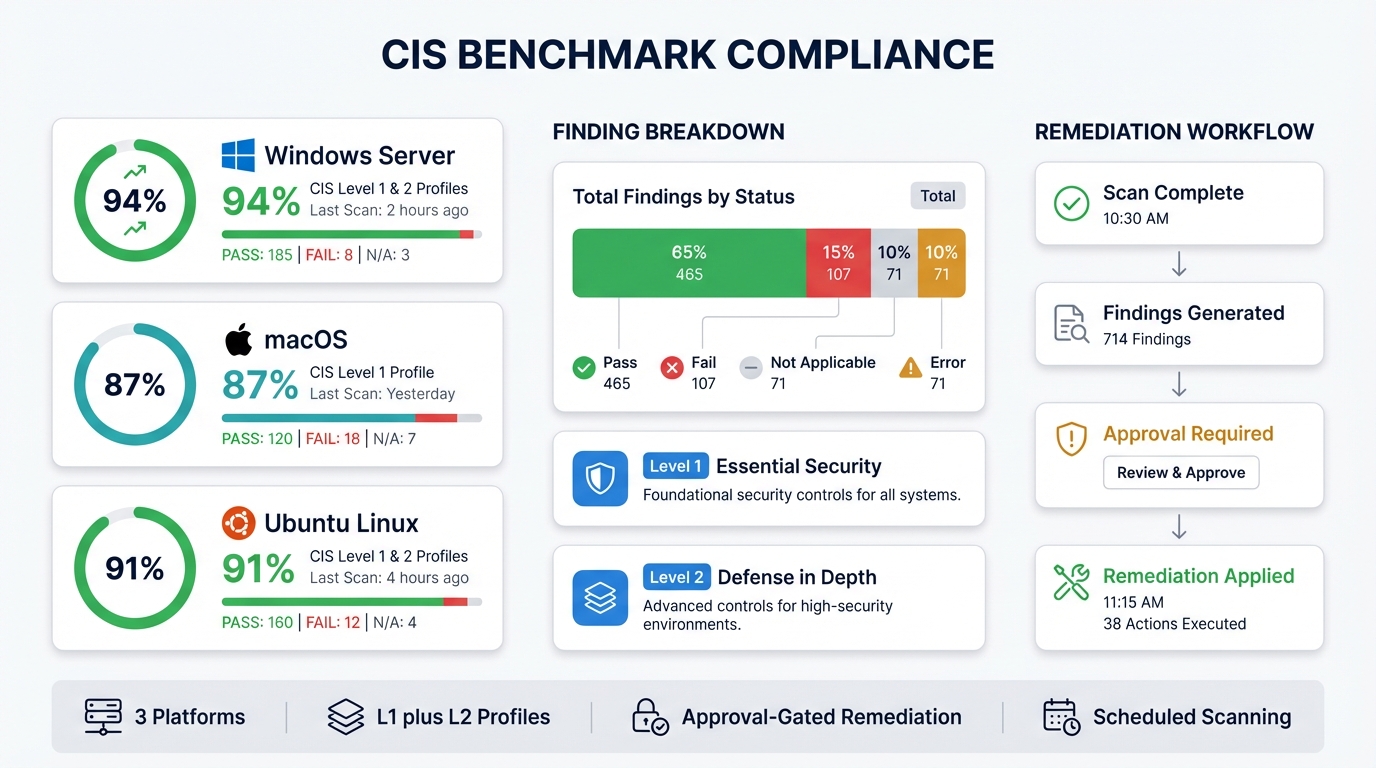
CIS Benchmark Dashboard
Compliance scoring, finding breakdowns, and approval-gated remediation across Windows, macOS, and Linux.
 View feature details
View feature details
How Compliance Automation Works
Four stages that turn raw endpoint data into audit-ready compliance evidence without manual effort.
Automated Data Collection
32 data pipelines feed compliance data from every managed endpoint. Hardware inventory, software state, configuration baselines, patch levels, account activity, and log streams are collected continuously without technician intervention.
Policy Enforcement
Configuration policies map directly to CIS Controls. Define your security baseline once and Breeze enforces it across every device in scope. Drift is detected in minutes, not quarters.
Posture Scoring
Real-time compliance scoring per device, per organization, and across your entire portfolio. Know exactly which controls are passing, which are drifting, and which need attention right now.
Evidence Generation
Audit-ready reports and evidence packages generated automatically. Timestamped enforcement records, configuration snapshots, and remediation logs ready for assessors without manual assembly.
Automated Data Collection
32 data pipelines feed compliance data from every managed endpoint. Hardware inventory, software state, configuration baselines, patch levels, account activity, and log streams are collected continuously without technician intervention.
Policy Enforcement
Configuration policies map directly to CIS Controls. Define your security baseline once and Breeze enforces it across every device in scope. Drift is detected in minutes, not quarters.
Posture Scoring
Real-time compliance scoring per device, per organization, and across your entire portfolio. Know exactly which controls are passing, which are drifting, and which need attention right now.
Evidence Generation
Audit-ready reports and evidence packages generated automatically. Timestamped enforcement records, configuration snapshots, and remediation logs ready for assessors without manual assembly.
CIS Controls Deep Dive Series
9 posts covering every control, the architecture behind compliance automation, and how to turn it into a managed service.
13 of 18 CIS Controls. Automatically. Here Is the Map.
32 Data Pipelines, 18 Security Controls: How Feature Design Maps to Compliance
The Foundation Controls: Asset, Software, Data, and Configuration
The Operational Controls: Accounts, Vulnerability, Logs, and Malware
The Response Controls: Recovery, Network, and Incident Response
How to Sell CIS Coverage as a Managed Service
The MSP That Can Prove Compliance Wins the Contract
Why Your Clients Keep Failing CIS Assessments (And Why It Is Not Their Fault)
The Hidden Cost of Your Compliance Stack
Stop assembling compliance evidence by hand
Deploy Breeze and get continuous CIS Controls enforcement, posture scoring, and audit-ready evidence across every managed endpoint. No add-ons, no per-device fees.