The MSP That Can Prove Compliance Wins the Contract
Five years ago, the MSP that answered the phone in thirty minutes won the deal. Three years ago, it was the MSP that had an EDR on every endpoint and could name their SOC provider. Today, the question that closes or loses enterprise and mid-market MSP contracts is harder to answer from memory: “Can you demonstrate continuous compliance with a security framework, and can you show me the evidence?”
Most MSPs have a tool for every part of that question. Almost none of them can actually answer it.
This is the shift that is restructuring the MSP market right now — not AI, not automation, not any particular security product. It is the shift from capability claims to verifiable evidence. And it is happening faster than most MSPs realize, driven by three forces that are reinforcing each other: cyber insurance underwriting requirements, client audit obligations, and a buyer population that has gotten sophisticated enough to know what questions to ask.
How We Got Here
The response time era made sense. Before centralized RMMs, before remote management at scale, fast human response to device problems was genuinely the differentiator. An MSP that could fix things faster than you could fix them yourself was worth paying for. SLAs around response time and resolution time were the right unit of measurement because response time was the constraint.
The EDR era followed the ransomware wave. After enough high-profile incidents, buyers started asking “what are you doing to prevent attacks, not just respond to them?” The tooling question — EDR, yes or no? Managed SOC, yes or no? MFA, yes or no? — became the qualifying round for MSP sales. MSPs that could check those boxes moved forward. MSPs that couldn’t were eliminated. For a few years, having the right vendor logos on your slide was enough.
That era is ending. The buyers who drove the EDR question have now had three to four years of experience with managed security services. They’ve been through insurance renewals. Some of them have been through audits. A meaningful subset of them have had incidents even with all the tools in place. They’ve learned that “we have an EDR” is not the same as “we have a documented, continuously verified security posture.”
The sophistication of the buyer has caught up with the complexity of the problem. And now the question they’re asking reflects that.
The Cyber Insurance Forcing Function
Cyber insurers have had four consecutive years of catastrophic loss ratios. The response has been systematic: coverage exclusions have gotten broader, premiums have increased, and underwriting requirements have gotten substantially more specific.
Many insurers are no longer accepting attestation as evidence of controls. They want documentation. They want to see that specific security controls are not just theoretically in place but verifiably operating across the environments they’re insuring. “Yes, we have patch management” is no longer sufficient for some carriers. They want to see patch compliance rates over time — what percentage of endpoints had critical patches applied within 48 hours, across the last 90 days.
This creates an immediate and concrete problem for MSPs. Their clients are coming to them before insurance renewals and asking for that documentation. The MSP that can produce it — pull up a 90-day patch compliance trend, export it to PDF, and hand it to the insurance broker — is removing a genuinely painful piece of the renewal process. They’re saving their client from having to answer difficult underwriter questions with “I’ll have to ask my IT provider and get back to you.”
The MSP that cannot produce that documentation is creating friction at exactly the moment when their client is most aware of the value question. Insurance renewals are high-stakes moments. If the MSP’s inability to produce evidence creates problems for the renewal — coverage denied, premium increased, coverage exclusions added — that failure will be remembered. It may be the trigger for a conversation that ends the relationship.
The insurers are effectively doing MSP sales qualification on behalf of their clients. They’re surfacing the question of whether the MSP can demonstrate what they claim. The MSPs who have built evidence pipelines are finding that insurance renewals have become a competitive advantage. The MSPs who haven’t are finding that they’ve become a liability at the most consequential moment of their client’s year.
What Happens in the Sales Meeting Now
“How do you handle CIS Control 4?” is a real question. It has been asked, in those terms, in MSP sales conversations. Not by enterprise buyers with a CISO on staff — by mid-market buyers who did their homework before the meeting, read the CIS Controls framework, and decided to understand what they were buying before they wrote a check.
There are two ways this question gets answered.
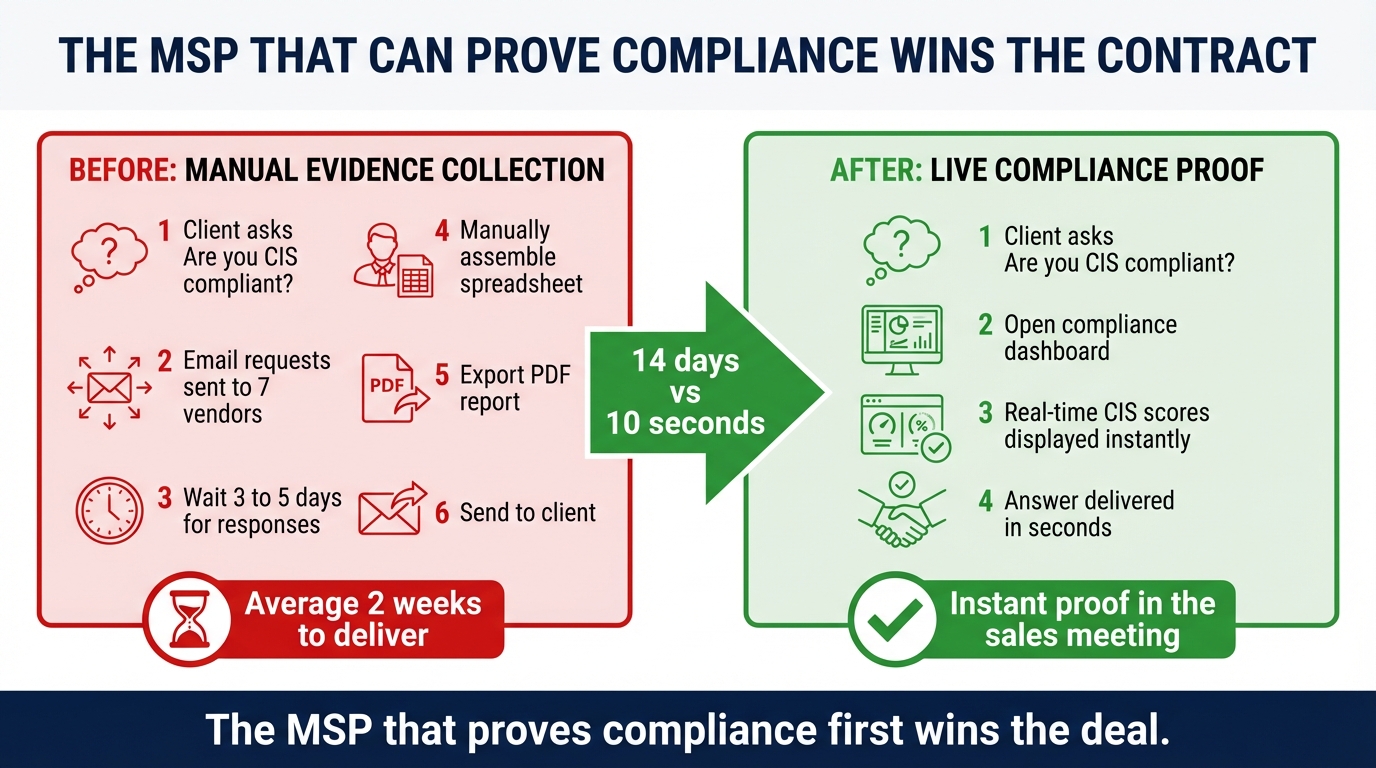
The first way: the MSP rep explains their patch management tool, their endpoint hardening baseline, their configuration management process. They describe, accurately, that they have the right tools and the right intent. They cannot show it live because the demo environment isn’t the client’s environment and they don’t have a dashboard that would make sense in this context. They say they can produce reports and schedule a follow-up.
The second way: the MSP pulls up a live compliance dashboard — not a screenshot, a live view — showing the current compliance posture across a sample environment. They show what a drift detection event looks like. They show the automated remediation log. They show the evidence history over the last 90 days. They show the report that gets generated for an auditor or insurer.
The second MSP wins the meeting. Not because their tools are necessarily better. Because they can demonstrate that their tools are continuously producing evidence, which is the actual answer to the question that was asked.
The shift isn’t that buyers are asking harder questions. The shift is that the questions they’re asking now require live proof rather than good explanations. An MSP that has built around continuous evidence collection can answer those questions instantly. An MSP that hasn’t built around it cannot answer them at all — they can only explain why the answer should exist.
The Switching Trigger Nobody Talks About
MSPs lose clients for the obvious reasons — service failures, price, relationship problems, acquisitions. But there is a less-discussed switching trigger that has been growing quietly: compliance audit events.
A client goes through a SOC 2 audit, or a HIPAA assessment, or a PCI compliance review. The auditor asks for evidence that their MSP has been maintaining continuous controls across their device fleet. The MSP cannot produce that evidence. The client fails the audit, or passes with significant findings, or delays the audit while trying to reconstruct documentation that was never systematically collected.
The client does not renew with that MSP. They go to market specifically looking for an MSP that can demonstrate compliance evidence capability. The MSP they select often wins on that single criterion — not on price, not on response time, not on the breadth of their service catalog. They win because they can pull up 12 months of patch compliance history, configuration drift events, and remediation logs in the first meeting and the previous MSP could not.
This is a structural shift in the switching dynamic. Price competition puts pressure on margins. Compliance capability competition puts pressure on platform investment. An MSP that has not built continuous evidence collection into their platform cannot compete for these clients, regardless of how good their people are or how reasonable their pricing is. The capability is either there or it isn’t, and mid-audit is a very bad time to discover it isn’t.
What Automated Evidence Collection Actually Looks Like
The operational description matters here because “compliance reporting” covers a wide range of actual capabilities, and the gap between the weakest and strongest implementations is significant.
A client asks: can you show me that all our devices have had critical patches applied within 48 hours for the last six months? With a real evidence pipeline, that question takes thirty seconds to answer — pull the patch compliance trend report, filter by severity, export. Without one, it takes hours: pull device-by-device patch logs from the RMM, cross-reference with the patch release dates, build a spreadsheet. If the data even exists in a queryable form, which it may not.
An insurer asks: do you have documentation that backup systems are tested? With automated verification logging, you show the weekly backup test history — success status, restore time, failure events, remediation. Without it, you’re asking a technician to reconstruct from memory and scattered notes.
An auditor asks: what devices were on your network on the fifteenth of last month? With a continuous device inventory, you pull the network baseline and device history, accurate to the hour. Without it, you’re guessing based on whatever state your RMM happened to be in at that moment.
These aren’t exotic requests. They’re the standard questions in any serious compliance review. The MSPs who have built around continuous evidence collection treat them as minor operational tasks. The MSPs who haven’t treat them as multi-hour research projects with uncertain outcomes.
The difference in client experience is stark. One MSP makes compliance audits easier. The other makes them harder. In a market where clients are increasingly subject to audit requirements, that difference is felt.
The Competitive Moat
Compliance evidence has an unusual property as a competitive differentiator: it compounds over time and it creates genuine switching costs.
A client receiving monthly compliance reports, built around your platform’s evidence collection, develops a historical record that lives in your system. After twelve months, they have a year of continuous patch compliance history, configuration drift logs, remediation records, and audit-ready documentation — all in a format that their auditors and insurers understand and have come to expect.
Switching MSPs means starting that history over. It means going to their next insurance renewal or audit without the evidence trail that the previous platform had accumulated. For a client in a regulated industry, or a client with a sophisticated compliance program, that is a real cost. Not a lock-in gimmick — an actual operational dependency on the evidence record that has been built.
The clients who care most about compliance evidence today are the clients worth building a business around. Regulated industries: healthcare, financial services, legal, manufacturing with OT environments. Companies that have been through acquisitions or are preparing for one. Companies that have experienced a security incident and rebuilt with discipline. These clients pay more, churn less, and generate referrals to organizations with similar profiles.
Building the compliance capability now is not just about winning the next deal. It is about selecting for the client base that makes the next five years of the business valuable.
The Question Is Already Being Asked
The framing of compliance as a future concern — something to build toward, something enterprise clients care about but not your current book — is increasingly wrong. Mid-market buyers are being pushed toward compliance frameworks by their insurers and their own clients. The hospital system that requires HIPAA compliance from its vendors passes that requirement to the vendors’ IT providers. The SaaS company pursuing SOC 2 for enterprise customers asks their MSP to demonstrate that their managed environment is covered under the attestation.
The compliance requirement is moving downstream. It was an enterprise concern three years ago. It is a mid-market concern today. In three more years, it will be a standard expectation in the SMB segment for any client that does business with a regulated industry or carries cyber insurance.
The MSPs who build continuous evidence collection into their platform now will have years of client history — and client confidence — by the time their competitors start to catch up. The ones who wait will be rebuilding from zero in a market that has moved on.
The question is already being asked in your prospect meetings. The MSP who can answer it instantly wins the room. The one who can’t explain that they’re working on it.
That explanation is not closing any deals.
Breeze RMM is built to close that gap — continuous evidence collection, automated remediation, and audit-ready reporting for MSPs managing compliance at scale. If you’re preparing for a client assessment or want to understand what your compliance evidence pipeline looks like today, we’re worth a conversation.