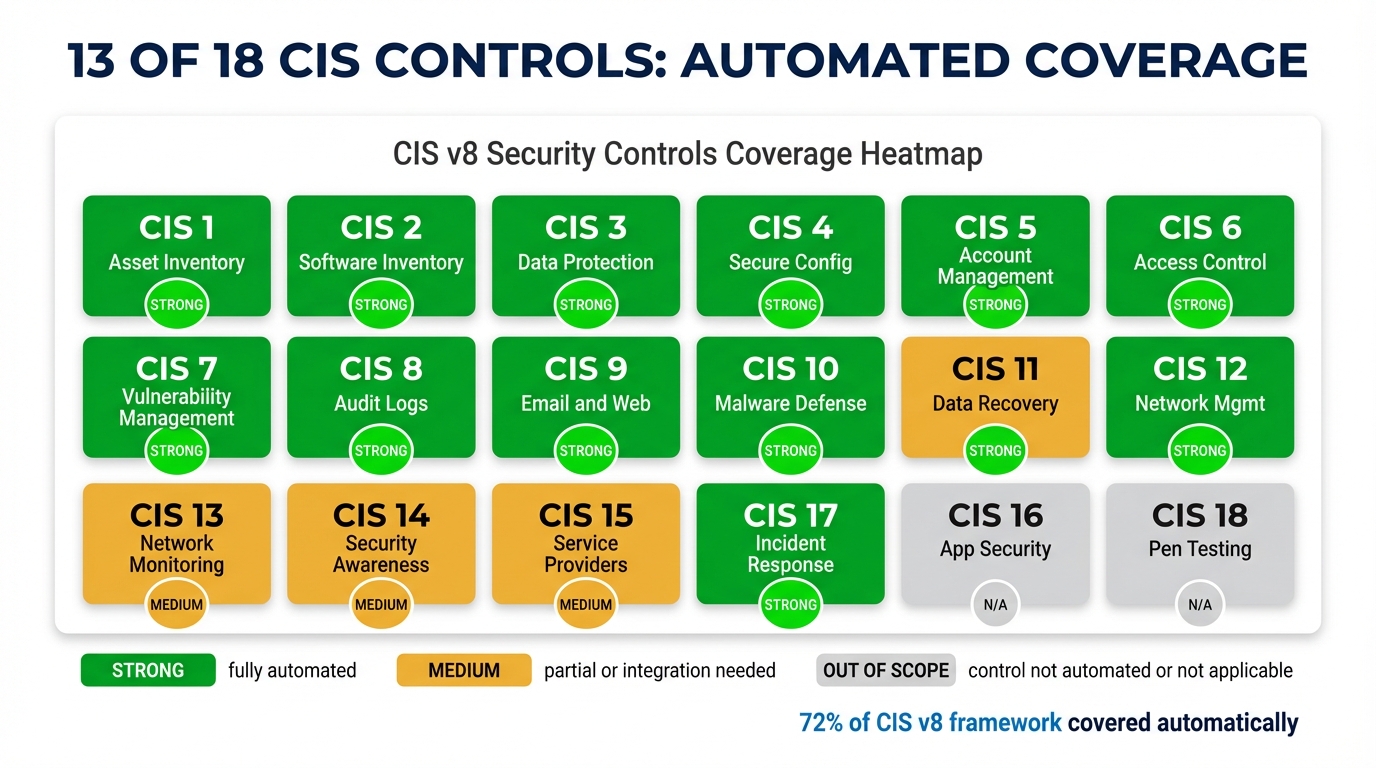
13 of 18 CIS Controls. Automatically. Here Is the Map.
Most organizations measure their CIS Controls coverage by asking the wrong question: “Do we have a tool that touches this area?” A firewall for network protection, an EDR for malware defenses, a patch management system for vulnerability management. The inventory looks complete. The controls look covered. The assessment arrives and something goes wrong.
The right question is different: “Is this control continuously enforced, with evidence, at every endpoint, automatically?” That’s a harder bar, and it’s the bar CIS Controls v8 is actually written against. The framework uses words like “actively managed,” “continuously maintained,” and “retained with defined retention.” It doesn’t say “periodically verified.” The difference between those two standards is the difference between compliance theater and a control environment that would survive a serious audit — or a serious incident.
This post maps Breeze’s coverage against the second, harder bar. Which controls are continuously enforced with automated evidence collection. Which require integrations with specialized platforms that no RMM can replicate. And the one control that is genuinely out of scope for any RMM in existence.
The Standard We’re Measuring Against
“Strong” coverage in this context means four things, all of which have to be true simultaneously:
- The control is continuously enforced — not checked quarterly, not surfaced in a dashboard, but enforced. Drift is detected and remediation is triggered without human intervention.
- Evidence is collected automatically. The system produces timestamped records of enforcement actions, not screenshots of dashboards.
- Drift detection exists. The platform knows when a device moves out of compliance after the initial hardening and flags or remediates it.
- Remediation is available with appropriate risk controls. The platform can initiate a corrective action — through its own capabilities or through a bidirectional integration — and that action goes through the same approval workflow as any other mutating operation.
“Medium” coverage means the platform covers the monitoring and visibility side of the control but relies on integrations with specialized platforms for the enforcement or training-delivery layer. This is an honest assessment. There are controls where the right tool is a dedicated GRC platform or a security awareness training provider, and the RMM’s job is to feed data into that system — not to replace it.
“N/A” appears exactly once. We’ll get to it.
The Coverage Matrix
| CIS Control | Coverage Level | How It’s Covered |
|---|---|---|
| 1. Asset Inventory | Strong | Continuous network scanning (BE-18), IP history tracking (BE-19), auto-discovery → auto-monitoring pipeline (BE-5) |
| 2. Software Inventory | Strong | Application allowlist/blocklist enforcement with auto-remediation (BE-15), browser extension risk classification (BE-27), software inventory with version tracking |
| 3. Data Protection | Strong | Sensitive data discovery — PII, PCI, PHI, credentials (BE-24), USB peripheral control with read-only enforcement (BE-25), encryption status monitoring (BE-9) |
| 4. Secure Configuration | Strong | Full CIS Benchmark assessment — 200+ checks on Windows, 100+ macOS, 150+ Linux (BE-26), audit policy baselines (BE-21), security posture scoring (BE-9) |
| 5. Account Management | Strong | Just-in-time privilege elevation with auto-revocation (BE-17), session tracking (BE-8), user risk scoring (BE-31) |
| 6. Access Control | Strong | Elevation request workflow (BE-17), RBAC across multi-tenant hierarchy |
| 7. Vulnerability Management | Strong | NVD-correlated CVE scanning against software inventory (BE-16), automated patch management |
| 8. Audit Log Management | Strong | Fleet-wide full-text log search (BE-20), audit policy enforcement (BE-21), agent diagnostic log shipping (BE-14) |
| 9. Email/Browser Protection | Strong | Browser extension risk classification with sideload detection (BE-27), DNS filtering integration — Umbrella, Cloudflare, DNSFilter (BE-28), Huntress email module (BE-22) |
| 10. Malware Defenses | Strong | Huntress integration — persistent foothold detection (BE-22), SentinelOne bidirectional API (BE-23), application control (BE-15) |
| 11. Data Recovery | Strong | Automated backup verification with test restores and RTO/RPO measurement (BE-29) |
| 12. Network Infrastructure | Strong | Network device config backup and firmware tracking (BE-30), network diagnostics (BE-4) |
| 13. Network Monitoring | Strong | Continuous network awareness and rogue device detection (BE-18), network diagnostics (BE-4), auto-discovery → monitoring (BE-5), DNS filtering (BE-28) |
| 14. Security Awareness | Medium | User risk scoring (BE-31), training platform integration (partial) |
| 15. Service Provider Mgmt | Medium | Multi-tenant architecture, integration audit trails |
| 16. Application Security | Medium | Application whitelisting (BE-15), CVE scanning (BE-16), browser extension control (BE-27) |
| 17. Incident Response | Strong | Full IR workflow — detection → containment → evidence → recovery → report (BE-32), Huntress/SentinelOne EDR integration (BE-22/23) |
| 18. Penetration Testing | N/A | Out of scope for any RMM — complementary service |
Where “Strong” Means What It Says
A few controls are worth walking through in detail, because the implementation specifics matter more than the label.
CIS Control 1: Asset Inventory
BE-18 runs continuous network scanning. Not on a schedule — continuously. When a new device joins a network segment, it’s detected, fingerprinted, and either matched to an existing inventory record or flagged as an unrecognized asset. BE-19 maintains IP history so that IP address reuse doesn’t create phantom duplicate entries. BE-5 completes the pipeline: auto-discovered devices move automatically into monitoring, so the inventory isn’t a static list that someone maintains manually — it’s a live record that the platform updates.
The standard for Control 1 is that every asset is accounted for and the inventory reflects current state. The common failure mode is point-in-time scanning that misses devices added between scan windows, or discovery tools that flag assets without automatically enrolling them. The auto-discovery → auto-monitoring pipeline closes both gaps.
CIS Control 4: Secure Configuration
BE-26 runs 200+ CIS Benchmark checks on Windows endpoints, 100+ on macOS, and 150+ on Linux. These aren’t custom baselines defined by the MSP — they map directly to published CIS Benchmark content, which means the evidence they produce maps to the same standard the assessor will use. BE-21 enforces audit policy baselines and detects when system audit settings drift from the defined configuration.
The reason this is “Strong” rather than “Medium” is drift detection and remediation. It’s not enough to run a benchmark assessment once and store the result. Control 4 requires a demonstrable process for detecting and addressing drift. When a device moves out of compliance — a Windows update re-enables a disabled service, a software install modifies a hardened registry key — that drift is detected and remediation is initiated. The evidence trail includes the detection timestamp, the remediation action, and the result.
CIS Control 7: Vulnerability Management
The NVD correlation in BE-16 matters more than it might appear. Many RMMs track installed software and separately track CVEs, but the gap between those two data sets is where vulnerabilities live. BE-16 correlates the software inventory directly against NVD data, so when a new CVE is published affecting a version of software that exists in the fleet, the exposure is identified without a manual cross-reference step. The patch management integration handles remediation. The combination produces what Control 7 actually requires: a process that continuously identifies vulnerable software and acts on it.
CIS Control 8: Audit Log Management
BE-20 provides fleet-wide full-text log search. This is a different capability from “we ship logs to a SIEM” — it’s native centralized log search that works across all agents without requiring an external log aggregation platform. BE-21 enforces the audit policy settings on Windows that determine what gets logged in the first place. BE-14 ships agent diagnostic logs. The combination covers the three components Control 8 actually requires: comprehensive logging, centralized collection, and searchable retention.
CIS Controls 9 and 10: The Integration Question
Controls 9 and 10 are where the integration quality matters as much as the feature list. Browser protection, email security, and malware defenses are areas where specialized tools — Huntress, SentinelOne, DNS filtering providers — provide capabilities that no RMM should try to replicate natively. The question is whether those integrations are first-class or superficial.
The Huntress integration (BE-22) and SentinelOne integration (BE-23) are bidirectional. They don’t just pull status data for display in a dashboard. They sync threat intelligence in both directions, and the platform can initiate actions through them — isolation, remediation, investigation — through the same workflow as any other platform action. Browser extension risk classification (BE-27) adds a layer that most security platforms don’t cover: identifying risky or sideloaded extensions before they become a compromise vector. DNS filtering (BE-28) integrates with Umbrella, Cloudflare, and DNSFilter, covering the network-level protection component of Control 9 without requiring a separate management pane.
CIS Control 17: Incident Response
BE-32 implements a structured IR workflow — detection, containment, evidence collection, recovery, and post-incident reporting — as a native platform feature. This matters because IR documentation is one of the areas where assessors most frequently find gaps. The incident happened, the response happened, but the evidence trail — who did what, when, in what order, with what outcome — exists in email threads and memory rather than a structured record. The platform workflow produces that record as a byproduct of the response process itself.
Where “Medium” Is the Honest Answer
CIS Control 14: Security Awareness Training
BE-31 covers user risk scoring — identifying users whose behavior patterns suggest elevated risk, tracking anomalous access, and surfacing that information in a usable format. This is the monitoring side of Control 14. The training delivery side requires integration with a dedicated security awareness training platform. No RMM covers that natively, and any that claims to is almost certainly providing a superficial wrapper around someone else’s content. The platform makes the integration accessible; the content and delivery remain with specialized providers.
CIS Control 15: Service Provider Management
The multi-tenant architecture enforces isolation between partners, organizations, sites, and devices. Integration audit trails track what third-party integrations have access to what data. The gap is that Control 15 also calls for formal service provider inventory, due diligence documentation, and risk assessment — areas that belong in a GRC platform, not an RMM. The platform provides the data foundation for that process, not the process itself.
CIS Control 16: Application Security
Application whitelisting (BE-15), CVE scanning (BE-16), and browser extension control (BE-27) cover the runtime and inventory sides of application security. The control also covers SAST, code review processes, and secure development lifecycle practices. Those are development process controls, not endpoint management controls. No RMM covers them, and none should. The “Medium” rating reflects genuine, useful coverage of the subset that falls within the RMM domain.
CIS Control 18: The One That’s Genuinely Out of Scope
CIS Control 18 covers penetration testing. Any platform claiming to automate penetration testing is not doing penetration testing. Pen testing requires human judgment — identifying what’s interesting, following threads, thinking like an attacker, understanding business context. Automated vulnerability scanning is useful and is covered under Control 7. It is not a substitute for adversarial human testing, and the distinction matters enough that claiming otherwise is a credibility problem for any platform that makes the claim.
Pen testing is a complementary service. The RMM’s job is to ensure that the findings from a pen test can be remediated efficiently and that the remediation produces evidence. That’s the right division of responsibility.
What the Map Actually Means
A coverage matrix is useful primarily for identifying where your gaps are, not for confirming that everything is fine. Thirteen of eighteen controls at “Strong” is a better starting position than most organizations have, but the controls at “Medium” still require real investment — in integrations, in specialized platforms, and in the processes that connect platform data to human decision-making.
The more important point is what “Strong” means in this context. It means the control is enforced continuously, evidence is collected automatically, drift is detected, and remediation is available. That’s the bar that separates continuous compliance from a compliant-looking dashboard that fails when an assessor asks for 90 days of evidence.
If you’re building a compliance program for a client that needs to demonstrate CIS Controls coverage — not just claim it — the question to ask about every control isn’t “which product covers this.” It’s “can I produce evidence that this was enforced, continuously, over the audit window?” The platforms and integrations listed here are designed to make that question answerable. The work of actually building the program around them is still your responsibility. But it’s significantly more tractable when the evidence is being collected automatically rather than assembled after the fact.
LanternOps, the cloud intelligence layer built on Breeze, surfaces the compliance evidence across this matrix in a format designed for vCISO workflows — normalized, queryable, and ready for audit export. For organizations working toward a formal CIS assessment, that’s the layer that turns continuous enforcement into demonstrable compliance.